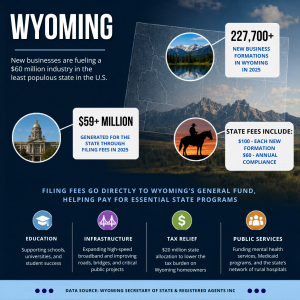
A report published by Research and Markets expects the global tokenization market will reach $2.25 billion by 2020. This tokenization will be at a Compound Annual Growth Rate (CAGR) of 22.4%.
“There is a constant pressure of managing sensitive data of consumers, along with the need to manage stringent compliances. This led enterprises to adopt tokenization solutions for critical information protection,” Research and Markets analysts stated in a press release.
“Cloud-based deployment is gaining high traction in the market. Cloud requires less capital, decreases operational and maintenance costs, and reduces the management’s efforts. Cloud tokenization solutions are available according to customer’s demand. This means a customer can start or stop any service, at will.”

As Research and Markets analysts explain, tokenization solutions will replace payment card data with a unique token. This will allow organizations to comply with the Payment Card Industry Data Security Standard (PCI DSS). It will also comply with the Health Insurance Portability and Accountability Act (HIPAA).
Payment security, user authentication, and compliance management use tokenization. The payment security application area is expected to dominate the tokenization market.
Table of Contents
ToggleA Changing Security Environment
Security will play a key role in changing the tokenization market landscape. E-commerce and the healthcare industry are driving the need for payment security. As such, cloud deployment is the fastest-growing application in the tokenization market. Organization gain increased scalability, speed, and 24/7 services. It also enhances management capabilities. In particular, Small & Medium-sized Enterprises (SMEs) use cloud deployment. It helps them avoid hardware, software, storage, and technical staff expenses.
Simply put, tokenization is going to completely disrupt the Banking, Financial Services. It will also change Insurance (BFSI), government, retail, healthcare, and IT and telecom. It’s in your best interest to learn about tokenization.
What is Tokenization and How Does it Work?
“The heart of tokenization is the token. A token is, very simply, a piece of data that stands in for another, more valuable piece of information,” explains Alex Pezold. Pezold is CEO at TokenEx (a cloud-based credit card tokenization and data vaulting service).
“Tokens have virtually no value on their own – they are only useful because they represent something bigger. A good analogy is a poker chip. Instead of filling a table with wads of cash (which can be easily lost or stolen), players use chips as placeholders. The chips can’t be used as money; they must be exchanged for it after the game.”
“Tokenization works by removing the valuable data from your environment and replacing it with these tokens. Most businesses hold at least some sensitive data within their systems. Data is credit card data, medical information, Social Security numbers, or anything requiring security and protection.” Pezold adds “Using tokenization, this data is taken out of your environment entirely. The data is replaced with tokens that are unique to each piece of information.”

Tokens replace a sensitive data element, like primary account number (PAN) data or credit card numbers. In the data’s place is a non-sensitive equivalent, which is referred to as a token. A token has no extrinsic or exploitable meaning or value.
The reason tokenization has become increasingly popular is because of data breaches. As Pezold explains, “if a data thief steals tokenized data, they really haven’t gotten anything but a bunch of useless tokens.” Additionally, tokenization is helping organizations reduce their compliance obligations.
Tokenization in Action
What does a token look like? There are two types of token formats: format preserving and non-format preserving.Format preserving tokens maintain the appearance of the original 16-digit payment card data. For example:
Payment Card Number: 4111 1111 1111 1111
Format Preserving Token: 4111 8765 2345 1111
Non-format preserving tokens do not resemble the original data at all and could include both alpha and numeric characters. For example:
Payment Card Number: 4111 1111 1111 1111
Non-format Preserving Token: 25c92e17-80f6-415f-9d65-7395a32u0223
Most organizations, however, prefer to use a format preserving tokens in order to avoid causing data validation issues with existing applications and business processes.
How exactly do tokens work? There are five steps in credit card processing:
- A credit card is swiped through a POS machine or the numbers are entered manually into an ecommerce site.
- The POS machine or ecommerce site sends the PAN to the credit card tokenization system.
- The tokenization system generates a string of 16 random characters that replace the PAN. It retrieves the associated token and records the correlation in the data vault.
- The token is returned to the POS terminal or commerce site and represents the customer’s credit card in the system.
- If the organization is using a payment processor’s tokenization solution, then the token is sent to the payment processor. They use the same tokenization technology to de-tokenize and view the original credit card number and process payment. If the organization is using a third-party tokenization solution, then the token goes to the third party. They de-tokeniz and send it to the payment processor for credit card processing.
A Brief History of Tokenization
The concept of tokenization isn’t exactly new. In fact, it’s been around for centuries. Take for for example the coin-like objects known as spintria during the Roman Empire. There was a copper farthing produced in England in the 17th Century, or more recently slot machine tokens. However, tokenization for the payment industry began in the 1970s.
“In databases, surrogate key values have been used since 1976. The key would isolate data associated with the internal mechanisms of databases. It also isolated their external equivalents for a variety of uses in data processing,” writes Joyrene Thomas for Payments Card & Mobile.
In 2001, TrustCommerce created the concept of Tokenization to protect sensitive payment data for one of their clients Classmates.com. Shift4 Corporation was the first to apply tokenization to payment card data. They released this to the public during an industry Security Summit in Las Vegas, Nevada in 2005. To comply with industry standards and government regulations, it now protects sensitive cardholder data. Apple Pay, Visa Token Service, American Express Token Service, and the MasterPass digital wallet have all breathed new life into tokenization.

What’s the Difference Between Tokenization and Encryption?
Tokenization and encryption secure transmitted or stored information. Organizations use tokenization and encryption for their data security strategies. However, there are some significant difference between the two.
Encryption, as defined by Stanford University’s encryption expert, “is the transformation of data into a form unreadable by anyone without a secret decryption key. Its purpose is to ensure privacy by keeping the information hidden from anyone for whom it is not intended. Even those who can see the encrypted data can’t decipher it. One may wish to encrypt files on a hard disk to prevent an intruder from reading them.”
Public-key cryptography increases security. No one needs to see or receive the private keys. The other advantage is to provide digital signatures.
However, there are some serious disadvantages of encryption as well. First, data encryption is reversible and can be eturned to its original, unencrypted form.
Encryption strength is based on the algorithm used to secure the data. A more complex algorithm creates stronger encryption that is more difficult to compromise, says Pezold.
Factors to Consider
“Another problem with encryption is that, because it’s reversible, the PCI Security Standards Council and other governing compliance entities still view encrypted data as sensitive data,” adds Pezold. As a result, organizations can expect significant capital expenditure in purchasing solutions to protect this encrypted data. Also, compliance costs can become a huge expense for businesses.
In contrast, tokenization doesn’t have these problems. That’s because tokenization doesn’t rely on encryption to protect data. Rather than securing information through a breakable algorithm, a tokenization system replaces sensitive data. The replacement is a one-to-one-mapped random data within your environment.
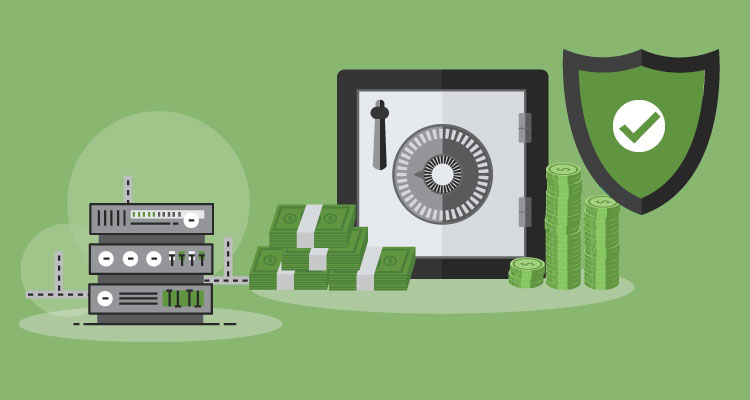
The token does not contain the original information. It’s simply a placeholder with no inherent value. Meanwhile, a different location secures the real sensitive information. This includes a secured offsite platform. Therefore, sensitive customer data does not enter or reside within your environment at any time.
Simply put, if a hacker breaks into your environment and steals tokens, they end up with nothing valuable.
Numerous Benefits
“The primary advantage of tokenization is that it keeps credit card data safe — both from internal and external threats. The payment processor is the only party that is able to decode the token. This security measure is extremely effective at reducing consumer credit card fraud,” states our partners over at BluePay.
Tokenization also benefits merchants. They don’t have to invest in as many resources to make your payment infrastructure secure. Instead, your entire system is PCI-compliant because you are not storing financial data.
Also, tokenization applies to any type of personally identifiable information. This includes patient records, employee files, usernames, passwords, email addresses, and customer accounts.
Tokenization also works with other types of payments besides credit cards. Tokenization works with cards such as gift cards, NFC payments, ACH transfers, and Apple Pay. Customer data is protect when they send or receive money.
Tokenization can used to securely store customer’s cards on file so that you can recharge their account. You can also issue refunds and set a recurring payment schedule.
Who Should be a Token Service Provider?
Rambus says that a “token service provider is an entity within the payments ecosystem. This entity provides payment tokens to any registered token requestors. The requestors include OEM Pay wallets or e-commerce merchants who hold card data on their systems.”
Token service providers “have the ability to issue and manage the entire lifecycle of payment credentials. They can implement tokenization to reduce payment card fraud and ensure transactions integrate with the existing authorization host.
The token service providers do this by converting or validating cryptograms, as well as performing processing checks.” They’re also responsible for the operation and maintenance of the token vault and deployment of security measures and controls.
The token service providers also have to keep the registration process of allowed token requestors. If you want to become a token service provider, then you must meet the classifications established by EMVCo, the global standards body.
But, should you become a token service provider? It depends on “the manner in which an issuer chooses to implement tokenization. This is because it’s dependent on its existing policy in terms of in-house versus outsourcing. This leaves wider commercial considerations.”
There are advantages and benefits for becoming a TSP. You’ll have “lower long term costs and the ability to maintain independence. You will also have flexibility to adapt and expand overall business strategy.”

How Many Credit Cards Can a Data Vault Hold?
The data vault is the keystone to the tokenization process. But, what would happen if a merchant takes billions of transactions each year? Would that affect the data vault?
To answer those question you need to understand the difference between single-use tokens and multi-use tokens.
- Single-use tokens represent a single transaction. This means that they processes faster than multi-use tokens.
- Multi-use tokens represent the same 16-digit PAN. They can be used for multiple transactions.
So, which should you use? It ultimately depends on your need for retaining tokens and plans for storage expansions.
Is Tokenization Right For Your Organization?
If you’re handling any sort of sensitive data then you should definitely use tokenization to reduce risk and secure data. Before you invest in tokenization, make sure that you consider the following:
- Storage pricing. If you want to host your own tokenization platform in-house, then you must plan for additional architecture. You’ll need memory storage that goes beyond the initial cost of implementation. There are still costs even if you use the cloud.
- Implementation. You also need to know where sensitive data exists in your environment. This handy card flow diagram can help with that.
- Choosing the right tokenization solution provider. Finally, you need to find the right partner. You limit yourself when your payment processor is your tokenization solution provider. That’s because you can only process with that processor. You should be able to work out a decent implementation deal. With third party PCI tokenization solutions like TokenEx, it’s easier to work with multiple payment processors.
Additional Facts
While a lot has been said about tokenization, there are still other facts that help you understand how it works and why you should consider it. Tokens need to be stored somewhere (local/session storage or cookies). They can expire like cookies, but you have more control. Use a marker cookie when local and session storage won’t work across domains.
Tokens are not silver bullets. Therefore, think about your authorization use cases carefully. There are pitfalls when implementing tokenization. Make sure that you partner with a vendor who understands how to implement tokenization correctly. They will need to understand technology as well as security, compliance, and risk.