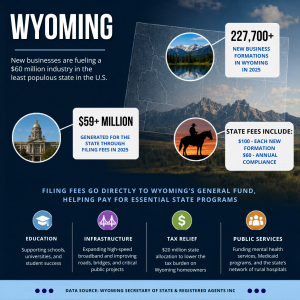
Investing in and trading cryptocurrencies has become more and more popular mainly due to stories of people who got back double or even triple the amount they put in.
These stories are, indeed, true. Take for example the case of Eddy Zillan who invested a few thousand dollars in crypto and became a millionaire.
Of course, people want to have the same success, just like Eddy. No surprise then that the crypto market gained 17 million verified users in 2018.
There are many opportunities to earn profits in the crypto market. But, there are also scams and other security issues that have plagued the industry over the years — including a recent case where a $65M Canadian crypto hacker was charged.
- In 2019, Bitrue, a Singapore-based crypto exchange platform was hacked for around $4.2 million worth of cryptocurrency assets.
- One phishing scam that went on for three years, starting in 2016, tricked many investors, and allegedly over $100million in cryptocurrency was stolen.
While there are still plenty of people who want to try their hand trading crypto, there are some who are hesitant simply because they are scared.
Now, what can you do to avoid falling for scams and compromising the security of your accounts?
Table of Contents
ToggleTips to Help You Secure Your Cryptocurrency
1. Always Check Your Account Activity
Have you ever made an audit of all your cryptocurrency wallets, logins, and other accounts that contain information related to your crypto assets?
If you haven’t done that, then you’re putting your accounts at risk.
To start, check your email inbox so you can see which crypto platforms you signed up for. You can write these on a piece of paper or keep a record of it in a place that you think is most secure for you.
Knowing all your accounts will help you monitor the activities and act immediately should there be something suspicious going on.
It’s simple but effective.
2. Check if an Initial Coin Offering (ICO) is Fake
Whilst investing and trading are different animals, ICOs cross into trader territory because marketing is directed at people with a little crypto experience. It’s tempting to invest in an ICO that promises great technology and high ROI.
But, this is where many rookie traders (and investors) get scammed. If you don’t know the red flags, chances are, you’ll become part of the statistics.
There are some things you can do to identify these fake ICOs:
- Check the website’s team members. Look for any information about the founders and their staff. Investigate their activities on social media accounts. If you see that their number of likes and followers they accrued doesn’t match their account activity, then that’s a red flag.
- Read their whitepaper. Check if it contains reliable resources, a sound roadmap for implementation, and a well-researched financial model.
- Ask for samples or code uploaded to repositories such as GitHub. If they cannot produce it, then it goes to show that no actual project or blockchain development is going on. You can hire a developer online to check it out if you don’t have the skills yourself.
Make sure that the ICO developers have set up a legitimate escrow service to receive investments. Be wary of those who are receiving funds through a personal cryptocurrency wallet.
It’s relatively easy to set up an ICO which is why scams have risen over the years.
The US Securities and Exchange Commission (USEC) even created a fake ICO to show investors the telltale signs of a fraudulent ICO.
When an offer seems too good, dig around for more information before making a move. If you are feeling FOMO through the marketing and not enough substance, walk away.
3. Use 2-Factor Authentication (2FA) and Restrict Your API Keys
Two-factor authentication helps add a layer of security to your account.
But, it is highly advised to not use the SMS 2FA as it can be intercepted. Rather, crypto enthusiasts suggest the Google Authenticator App because it can be used offline and it is local to your device.
If you’re using a third-party software to help your trades, then it would be best if you place restrictions on your API keys so that it will only work with specific IP addresses. That way, you’re assured no one will be able to touch your account even if they manage to find your secret keys.
4. Don’t fall for a phishing email
Hackers nowadays are smarter when it comes to phishing for information.
That’s why you need to be extra vigilant whenever you receive emails with external links. Oftentimes, these phishing emails are designed to look like a legitimate company and may be tricky to detect.
Before clicking any external link or giving personal information, check the domain name. Legitimate companies use their domain name to send emails.
Hackers tend to use domain names that look almost similar to the company. For example, an email with the domain @coinbase.org may be easily mistaken for @coinbase.com.
Also, if the email asks you to confirm personal information, be wary. Search for the organization and contact them directly. Don’t use any form of communication indicated in the email.
Be suspicious as well of any attachment in the email as it may be a malware. This is usually used by scammers to get into a computer and steal information.
Lastly, don’t send cryptocurrency to a wallet through email. ICOs and crypto exchange platforms won’t ask you to transfer crypto using this method.
5. Don’t store all of your money in an exchange
Over the years, some crypto exchanges have become victims of hacking attacks and other security issues. This resulted in many of their user accounts being frozen or worse, compromised.
That’s why there is no guarantee that your tokens can be safely stored in a crypto exchange platform. It should be stored in a private wallet.
There are four different types of wallets: paper wallet, hot wallet, mobile wallets, and cold wallets.
In the crypto world, it is highly recommended to have a cold wallet, also known as a hardware wallet. It has a Secure Element (SE) chip to secure your keys in an offline device.
Since it is offline, your information is less vulnerable to potential hacks.
Plus, the microprocessor embedded in the device remains offline even when connected to the internet. This means that even if the computer has malware, your private keys won’t be compromised.
Some of the hardware wallets you might want to consider are:
- Ledger Nano S
- Trezor One
- KeepKey
Side note: It’s perfectly normal for traders to leave their trading funds on the exchange for convenience (it saves sending it all forwards and backwards each day). If you are happy with the risk go for it, but remove your profits regularly and keep those offline so that you are only risking an amount you can face losing.
6. Use software to hide your digital footprint
A digital footprint pertains to all the traces of your online activity. This includes your social media posts, comments, cookies, IP address, and login details.
Hackers can use these traces to access your personal information. You don’t want this to happen and risk compromising the security of your crypto assets.
That’s why it is recommended to use a Virtual Private Network (VPN) to hide your identity while browsing and keep your online activities away from prying eyes.
This is very easy to do. All you need is to download a reputable VPN program, install it on your device, and run it.
With this, you’re making yourself much more invisible online, encrypting your data, and masking your IP address.
Cryptocurrency Security Continues to Evolve
Security in the cryptocurrency world is not only the responsibility of the users but also service providers as well.
Fortunately, over the years, innovations across blockchain technology have allowed cryptocurrency service providers to step up when it comes to user security.
Recently the ETH network saw a $5.2 million fee charged to an exchange. After some investigation, it was theorized that this was a blackmail attempt.
The hackers were able to access the exchange’s funds but they could not transfer any of it away because of the multiple security measures set in place.
Overall, account security is a two-way street where the user has to take precautionary measures and for the software company to fix all vulnerabilities in their system.
Just keep in mind that unlike normal banks/savings in Europe, you are not guaranteed to get some money back if there is a hack or other fraud.
The Golden Rule
Quite simply, don’t be naive. It’s 2020 and hackers are much more sophisticated (even if they live in their mum’s basement) so don’t make it easy for them.
When you leave your house you probably don’t leave the doors unlocked. The same goes for your financial assets. Simple steps to take such as keeping your crypto in a cold wallet, leaving only your trading balance on the exchange, and regularly doing account audits will help you become more secure in the world of crypto trading.